As a very young kid, when I learned how to fish, I was hooked and it quickly became one of my favorite pastimes. My family had a camp that introduced me to the lake life, and before I knew it I was hooked on dragging a line, digging for night crawlers, and hand carving hula poppers out of wood.
My first winter of ice fishing occurred when I was about eight years old, and I will never forget it. We fished like the above image, but we used a flag system as well. If you have never been ice fishing, the flag system requires you to set the line in a cross with a flag, when you catch something the flag pops up.
Fast forward to my older self and the word fishing has a much less pleasant counterpart and it’s called Phishing.
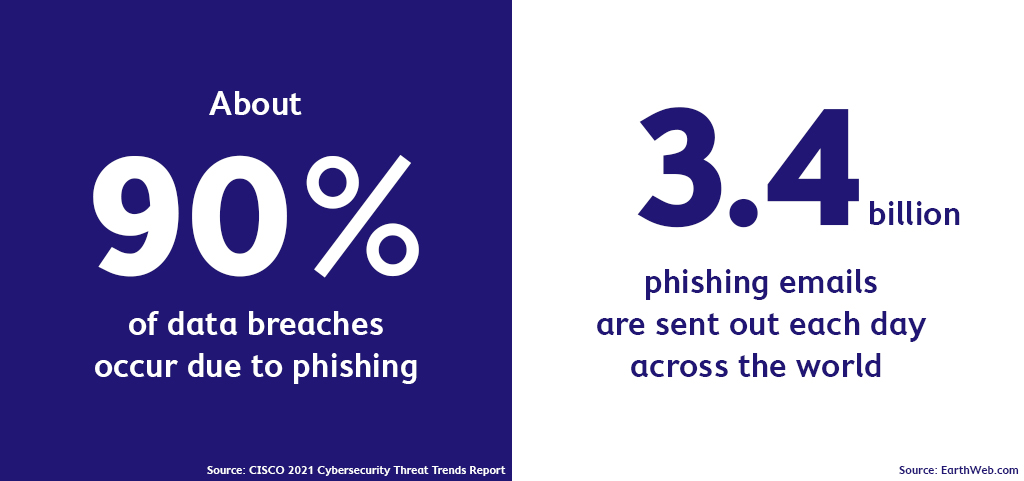
Phishing is a term used for gathering sensitive information, mostly via email, to be sold on the Dark Web. Phishing can also include links and attachments that contain malware or Ransomware which reeks havoc on your computer and network, compromising your data. This certainly does not have the same calming effect as the fishing I remember.
But, fear not, I’m going to provide you with five indicators that you may have received a Phishing email. Let’s visualize these as the ice fishing flags, except these are things you don’t want to catch – like that big, scary shark!
Red Flag 1: Intimidation or Rushing
If you receive an email unexpectedly that is requesting information, money, or other actions in an unusually short period of time, then, be suspicious. Begin to evaluate the email for the other red flags listed here. By rushing or intimidating you, email hackers are hoping that you won’t take time to scrutinize the email for flaws; don’t fall into this trap. Be alert, aware and thorough as you look for Phishing emails.
Red Flag 2: Small Mistakes
Emails with poor grammar or illogical sentence sequence should be evaluated. Vague headers or generic greetings, such as “Hello Customer,” could be a phishing email indicator. Additionally, the “From” email address could be very similar to the contact. By using letters that appear similar, such as an ‘rn’ instead of an ‘m,’ hackers can better fool you and have the opportunity to gain valuable information and data. Pay attention to sender information and the overall look and feel of emails you receive.
Red Flag 3: Requests for Private or Sensitive Information
If someone requests private or sensitive information, this should raise a red flag. These requests can be elaborate and seem valid at first, but you have to evaluate if the requested information should be sent at all. A common situation we encounter is a CEO asks for information that he should already possess or know. Phishing emails requesting sensitive data will probably be coupled with rushing and other red flags.
Red Flag 4: Requests to Open an Email Attachment

Email attachments allow hackers to run malicious software when you open or download the attachment. If you receive an email attachment that you weren’t expecting, has an odd file name, or appears to be coming from someone who doesn’t normally send you files, begin searching for other red flags to determine if the email is malicious. Do not open or download the attachment until you have verified with your IT or security resource that the email is not malicious.
Red Flag 5: Spoofed URLs and Hyperlinks
Hackers are skilled at making email addresses and hyperlinks look like something they’re not. If you’re suspicious of an email, hover over the link – without clicking – to see if the web address matches what is listed. For spoofed email addresses, click to reply to the email and check the email address in the “To” field to determine if it is correct for that contact.
By being vigilant and aware, you can help prevent irreversible damage to your business from malware, Ransomware and viruses delivered through Phishing and Spear Phishing emails. Nobody wants to catch a shark.
Stay Ahead of Phishing Attacks
If you need help implementing more security elements to help protect you against malicious attacks, or you’re interested in participating in a security training session, contact our team.